- Cryptographic Key Generation From Voice 2016
- Cryptographic Key Generation From Voice Download
- Cryptographic Key Generation From Voice Free
- Cryptographic Key Management Policy
- Cryptographic Key Generation From Voice Free
- Cryptographic Key Management System
Results 1 - 10 of 16
- In this thesis, we present results of an experimental study in order to generate a secure cryptographic key from the user’s voice which is to be shared between two mobile devices. We identified two security threats related to this problem, discussed the challenges to design the key generation/sharing mechanism, and proposed a new protocol based on bloom filters that.
- Cryptographic key generation from voice.
Voice-generated cryptographic keys In this paper, we advocate research into the generation of cryptographic keys from voice input. We are primarily interested in keys that can be temporally reproduced on the same device from the same user’s voice, and that are unguessable to an attacker who captures that device. Proposed voice-based cryptographic key generation. In which each biometric feature is conceptually contributed to one bit of the cryptographic key. Similarly, Jermyn et al. 2 proposed to use hand-drawn sketch to generate passwords according to the position and timing of the sketch drawing. Soutar 3 proposed the Biometric et al. The TCE 500/B is a narrow-band crypto terminal for secure voice and data communication providing end-to-end encryption between users in any type of telephone network - Photos: NSPA NSPA provides follow-on logistic support for NATO funded and non-NATO funded communication and information systems.
The Practical Subtleties of Biometric Key Generation
- In Proceedings of the 17 th Annual USENIX Security Symposium, 2008
'.. The inability of humans to generate and remember strong secrets makes it difficult for people to manage cryptographic keys. To address this problem, numerous proposals have been suggested to enable a human to repeatably generate a cryptographic key from her biometrics, where the strength of the key ..'
Abstract - Cited by 25 (2 self) - Add to MetaCart
Cryptographic Key Generation From Voice 2016
The inability of humans to generate and remember strong secrets makes it difficult for people to manage cryptographic keys. To address this problem, numerous proposals have been suggested to enable a human to repeatably generate a cryptographic key from her biometrics, where the strength of the key rests on the assumption that the measured biometrics have high entropy across the population. In this paper we show that, despite the fact that several researchers have examined the security of BKGs, the common techniques used to argue the security of practical systems are lacking. To address this issue we reexamine two well known, yet sometimes misunderstood, security requirements. We also present another that we believe has not received adequate attention in the literature, but is essential for practical biometric key generators. To demonstrate that each requirement has significant importance, we analyze three published schemes, and point out deficiencies in each. For example, in one case we show that failing to meet a requirement results in a construction where an attacker has a 22 % chance of finding ostensibly 43-bit keys on her first guess. In another we show how an attacker who compromises a user’s cryptographic key can then infer that user’s biometric, thus revealing any other key generated using that biometric. We hope that by examining the pitfalls that occur continuously in the literature, we enable researchers and practitioners to more accurately analyze proposed constructions. 1
(Show Context)
Biometric authentication revisited: Understanding the impact of wolves in sheep’s clothing
- In Proceedings of the 15 th Annual Usenix Security Symposium, 2006
'.. Biometric security is a topic of rapidly growing importance, especially as it applies to user authentication and key generation. In this paper, we describe our initial steps towards developing evaluation methodologies for behavioral biometrics that take into account threat models which have largely ..'
Abstract - Cited by 21 (10 self) - Add to MetaCart
Biometric security is a topic of rapidly growing importance, especially as it applies to user authentication and key generation. In this paper, we describe our initial steps towards developing evaluation methodologies for behavioral biometrics that take into account threat models which have largely been ignored. We argue that the pervasive assumption that forgers are minimally motivated (or, even worse, naïve), or that attacks can only be mounted through manual effort, is too optimistic and even dangerous. To illustrate our point, we analyze a handwriting-based key-generation system and show that the standard approach of evaluation significantly overestimates its security. Additionally, to overcome current labor-intensive hurdles in performing more accurate assessments of system security, we present a generative attack model based on concatenative synthesis that can provide a rapid indication of the security afforded by the system. We show that our generative attacks match or exceed the effectiveness of forgeries rendered by the skilled humans we have encountered. 1
Forgery Quality and its Implications for Behavioral Biometric Security
- IEEE Transactions on Systems, Man and Cybernetics (Special Edition
'.. Abstract — Biometric security is a topic of rapidly growing importance in the areas of user authentication and cryptographic key generation. In this paper, we describe our steps toward developing evaluation methodologies for behavioral biometrics that take into account threat models which have been ..'
Abstract - Cited by 11 (4 self) - Add to MetaCart
Abstract — Biometric security is a topic of rapidly growing importance in the areas of user authentication and cryptographic key generation. In this paper, we describe our steps toward developing evaluation methodologies for behavioral biometrics that take into account threat models which have been largely ignored. We argue that the pervasive assumption that forgers are minimally motivated (or, even worse, naïve) is too optimistic and even dangerous. Taking handwriting as a case in point, we show through a series of experiments that some users are significantly better forgers than others, that such forgers can be trained in a relatively straightforward fashion to pose an even greater threat, that certain users are easy targets for forgers, and that most humans are a relatively poor judge of handwriting authenticity and hence their unaided instincts cannot be trusted. Additionally, to overcome current labor-intensive hurdles in performing more accurate assessments of system security, we present a generative attack model based on concatenative synthesis that can provide a rapid indication of the security afforded by the system. We show that our generative attacks match or exceed the effectiveness of forgeries rendered by the skilled humans we have encountered. I.
(Show Context)
Towards Practical Biometric Key Generation with Randomized Biometric Templates
'.. Although biometrics have garnered significant interest as a source of entropy for cryptographic key generation, recent studies indicate that many biometric modalities may not actually offer enough uncertainty for this purpose. In this paper, we exploit a novel source of entropy that can be used with ..'
Abstract - Cited by 10 (0 self) - Add to MetaCart
Although biometrics have garnered significant interest as a source of entropy for cryptographic key generation, recent studies indicate that many biometric modalities may not actually offer enough uncertainty for this purpose. In this paper, we exploit a novel source of entropy that can be used with any biometric modality but that has yet to be utilized for key generation, namely associating uncertainty with the way in which the biometric input is measured. Our construction poses only a modest requirement on a user: the ability to remember a low-entropy password. We identify the technical challenges of this approach, and develop novel techniques to overcome these difficulties. Our analysis of this approach indicates that it may offer the potential to generate stronger keys: In our experiments, 40 % of the users are able to generate keys that are at least 2 30 times stronger than passwords alone. Categories and Subject Descriptors E.3 [Data Encryption]; H.1 [Models and Principles]: User/Machine
(Show Context)
Secret locking: Exploring new approaches to biometric key encapsulation
- Proc. of the 2nd Intern. Conf. on e-Business and Telecommunications (ICETE 2005, 2005
'.. Abstract: Biometrics play an increasingly important role in the context of access control techniques as they promise to overcome the problems of forgotten passwords or passwords that can be guessed easily. In this paper we introduce and provide a formal definition of the notion of secret locking whi ..'
Abstract - Cited by 2 (1 self) - Add to MetaCart
Abstract: Biometrics play an increasingly important role in the context of access control techniques as they promise to overcome the problems of forgotten passwords or passwords that can be guessed easily. In this paper we introduce and provide a formal definition of the notion of secret locking which generalizes a previously introduced concept for cryptographic key extraction from biometrics. We give details on an optimized implementation of the scheme which show that its performance allows the system for use in practice. In addition, we introduce an extended framework to analyze the security of the scheme. 1
(Show Context)
The Case for Replacing Passwords with Biometrics
'.. Abstract—The threat of malware and phishing is engulfing the web. It is expected to be an even greater threat in the mobile context, as battery power limitations and the lack of screen real estate of handsets tie the hands of anti-virus methods and user messaging methods, and people’s continuous han ..'
Abstract - Cited by 2 (1 self) - Add to MetaCart
Abstract—The threat of malware and phishing is engulfing the web. It is expected to be an even greater threat in the mobile context, as battery power limitations and the lack of screen real estate of handsets tie the hands of anti-virus methods and user messaging methods, and people’s continuous handset connectivity makes them more vulnerable to abuse. This paper argues that biometric methods, such as fingerprinting methods, could address a large part of this towering threat- but only if properly architected. We describe an architecture that is practically attainable and which would address the problem in a meaningful way, and argue that this is a promising direction – both in terms of security and usability. Keywords-authentication; biometrics; fraud; malware. I.
(Show Context)
Robust Techniques for Evaluating Biometric Cryptographic Key Generators
'.. Humans are unable to generate and remember strong secrets, and thus have difficulty managing cryptographic keys. To address this problem, numerous proposals have been suggested to enable people to reliably generate high-entropy cryptographic keys from measurements of their physiology or behavior. Ty ..'
Abstract - Cited by 1 (1 self) - Add to MetaCart
Humans are unable to generate and remember strong secrets, and thus have difficulty managing cryptographic keys. To address this problem, numerous proposals have been suggested to enable people to reliably generate high-entropy cryptographic keys from measurements of their physiology or behavior. Typically, evaluators argue that these Biometric Cryptographic Key Generators (BKGs) achieve some notion of security, for example, that the biometric input resists forgery, or that the keys have high entropy. Unfortunately, despite these arguments, many BKGs succumb to attacks in practice. The goal of this work is to understand why typical security arguments fail to identify practical attacks. We revisit the security requirements of BKGs and show that common arguments overlook practical subtleties. We provide examples of such oversights by examining three general classes of adversaries. First, we study the impact of humans who can replicate other users ’ biometrics with high accuracy, and demonstrate why typical evaluation techniques fail to identify these forgers. Second, we explore Generative techniques that combine information about a target user with population statistics to create forgeries. We show that these forgeries can subvert BKGs with high likelihood. Third, we propose an
Evaluating Biometric Security: Understanding the Impact of Wolves in Sheep’s Clothing
'.. Growing interest in biometric security has resulted in much work on systems that attempt to exploit the individuality of human behavior. In this paper, we survey our recent research examining issues arising when such biometrics are to be used for authentication or cryptographic key generation. We pr ..'
Abstract - Cited by 1 (1 self) - Add to MetaCart
Growing interest in biometric security has resulted in much work on systems that attempt to exploit the individuality of human behavior. In this paper, we survey our recent research examining issues arising when such biometrics are to be used for authentication or cryptographic key generation. We propose steps towards the development of more rigorous evaluation methodologies for behavioral biometrics that take into account threat models previously ignored in the literature. The pervasive assumption that adversaries are minimally motivated (or, even worse, naïve), or that attacks can only be mounted through manual effort, is too optimistic and even dangerous. The discussion is illustrated by summarizing our analysis of a handwriting-based key generation system showing that the standard evaluation methodology significantly overestimates its security. We also present an overview of our work on fully automated (generative) attack models that can be nearly as effective as skilled human forgers and thus present both a serious threat as well as a potential tool for improving the testing of biometric systems.
Cryptographic Key Generation From Voice Download
(Show Context)
Cryptographic Key Generation From Voice Free
BIOMETRICS FOR COMPUTER SECURITY AND CRYPTOGRAPHY
'.. In the last decade of computer security, using biometrics for various types of security problems becomes more and more popular. The uniqueness of biometrics for any specific humanbeing makes the identification system more secure. Biometrics are widely used in person identification and verification. ..'
Abstract - Cited by 1 (0 self) - Add to MetaCart
In the last decade of computer security, using biometrics for various types of security problems becomes more and more popular. The uniqueness of biometrics for any specific humanbeing makes the identification system more secure. Biometrics are widely used in person identification and verification. But using biometrics by means of cryptography is a new research area and there is less work in literature. In this paper we give a brief explanation of biometric cryptography approaches and algorithms which use various biometric data. We basically touch the use of keystroke dynamics, speech and 2D biometric data (such as fingerprint, palmprint, face,..etc).
(Show Context)
Speech Biometric Mapping for Key Binding Cryptosystem
'.. We propose a new scheme to transform speech biometric measurements (feature vector) to a binary string which can be combined with a pseudo-random key for a cryptographic purpose. We utilize Dynamic Time Warping (DTW) in our scheme. The challenge of using DTW in a cryptosystem is that a template must ..'
Abstract - Add to MetaCart
We propose a new scheme to transform speech biometric measurements (feature vector) to a binary string which can be combined with a pseudo-random key for a cryptographic purpose. We utilize Dynamic Time Warping (DTW) in our scheme. The challenge of using DTW in a cryptosystem is that a template must be useful to create a warping function, while it must not be usable for an attacker to derive the cryptographic key. In this work, we propose a hardened template to address these problems. We evaluate our scheme with two speech datasets and compare with DTW, VQ, and GMM speaker verifications. The experimental results show that the performance of the proposed scheme outperforms VQ and GMM. It is slightly degraded when compared to the DTW speaker verification. The EERs against attackers utilizing the hardened template are 0 % both datasets.
In cryptography, a key is a piece of information (a parameter) that determines the functional output of a cryptographic algorithm. For encryption algorithms, a key specifies the transformation of plaintext into ciphertext, and vice versa for decryption algorithms. Keys also specify transformations in other cryptographic algorithms, such as digital signature schemes and message authentication codes.[1]
Need for secrecy[edit]
In designing security systems, it is wise to assume that the details of the cryptographic algorithm are already available to the attacker. This is known as Kerckhoffs' principle — 'only secrecy of the key provides security', or, reformulated as Shannon's maxim, 'the enemy knows the system'. The history of cryptography provides evidence that it can be difficult to keep the details of a widely used algorithm secret (see security through obscurity). A key is often easier to protect (it's typically a small piece of information) than an encryption algorithm, and easier to change if compromised. Thus, the security of an encryption system in most cases relies on some key being kept secret.[2]
Trying to keep keys secret is one of the most difficult problems in practical cryptography; see key management. An attacker who obtains the key (by, for example, theft, extortion, dumpster diving, assault, torture, or social engineering) can recover the original message from the encrypted data, and issue signatures.
Key scope[edit]
Keys are generated to be used with a given suite of algorithms, called a cryptosystem. Encryption algorithms which use the same key for both encryption and decryption are known as symmetric key algorithms. A newer class of 'public key' cryptographic algorithms was invented in the 1970s. These asymmetric key algorithms use a pair of keys—or keypair—a public key and a private one. Public keys are used for encryption or signature verification; private ones decrypt and sign. The design is such that finding out the private key is extremely difficult, even if the corresponding public key is known. As that design involves lengthy computations, a keypair is often used to exchange an on-the-fly symmetric key, which will only be used for the current session. RSA and DSA are two popular public-key cryptosystems; DSA keys can only be used for signing and verifying, not for encryption.
Ownership and revocation[edit]
Part of the security brought about by cryptography concerns confidence about who signed a given document, or who replies at the other side of a connection. Assuming that keys are not compromised, that question consists of determining the owner of the relevant public key. To be able to tell a key's owner, public keys are often enriched with attributes such as names, addresses, and similar identifiers. The packed collection of a public key and its attributes can be digitally signed by one or more supporters. In the PKI model, the resulting object is called a certificate and is signed by a certificate authority (CA). In the PGP model, it is still called a 'key', and is signed by various people who personally verified that the attributes match the subject.[3]
In both PKI and PGP models, compromised keys can be revoked. Revocation has the side effect of disrupting the relationship between a key's attributes and the subject, which may still be valid. In order to have a possibility to recover from such disruption, signers often use different keys for everyday tasks: Signing with an intermediate certificate (for PKI) or a subkey (for PGP) facilitates keeping the principal private key in an offline safe.
Deleting a key on purpose to make the data inaccessible is called crypto-shredding.
Key sizes[edit]
Cryptographic Key Management Policy
For the one-time pad system the key must be at least as long as the message. In encryption systems that use a cipher algorithm, messages can be much longer than the key. The key must, however, be long enough so that an attacker cannot try all possible combinations.
A key length of 80 bits is generally considered the minimum for strong security with symmetric encryption algorithms. 128-bit keys are commonly used and considered very strong. See the key size article for a more complete discussion.
The keys used in public key cryptography have some mathematical structure. For example, public keys used in the RSA system are the product of two prime numbers. Thus public key systems require longer key lengths than symmetric systems for an equivalent level of security. 3072 bits is the suggested key length for systems based on factoring and integer discrete logarithms which aim to have security equivalent to a 128 bit symmetric cipher. Elliptic curve cryptography may allow smaller-size keys for equivalent security, but these algorithms have only been known for a relatively short time and current estimates of the difficulty of searching for their keys may not survive. As early as 2004, a message encrypted using a 109-bit key elliptic curve algorithm had been broken by brute force.[4] The current rule of thumb is to use an ECC key twice as long as the symmetric key security level desired. Except for the random one-time pad, the security of these systems has not been proven mathematically as of 2018, so a theoretical breakthrough could make everything one has encrypted an open book (see P versus NP problem). This is another reason to err on the side of choosing longer keys.
Key choice[edit]
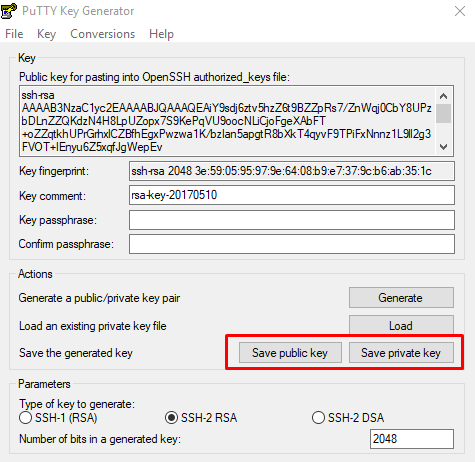
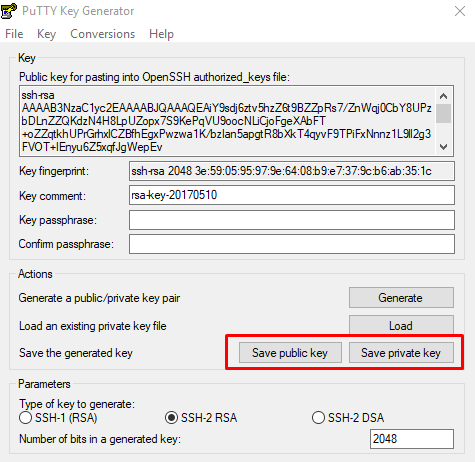
To prevent a key from being guessed, keys need to be generated truly randomly and contain sufficient entropy. The problem of how to safely generate truly random keys is difficult, and has been addressed in many ways by various cryptographic systems. Generate ssh key github. There is a RFC on generating randomness (RFC 4086, Randomness Requirements for Security). Some operating systems include tools for 'collecting' entropy from the timing of unpredictable operations such as disk drive head movements. For the production of small amounts of keying material, ordinary dice provide a good source of high quality randomness.
Key vs password[edit]
For most computer security purposes and for most users, 'key' is not synonymous with 'password' (or 'passphrase'), although a password can in fact be used as a key. The primary practical difference between keys and passwords is that the latter are intended to be generated, read, remembered, and reproduced by a human user (though the user may delegate those tasks to password management software). A key, by contrast, is intended for use by the software that is implementing the cryptographic algorithm, and so human readability etc. is not required. In fact, most users will, in most cases, be unaware of even the existence of the keys being used on their behalf by the security components of their everyday software applications.
Cryptographic Key Generation From Voice Free
If a passwordis used as an encryption key, then in a well-designed crypto system it would not be used as such on its own. This is because passwords tend to be human-readable and, hence, may not be particularly strong. To compensate, a good crypto system will use the password-acting-as-key not to perform the primary encryption task itself, but rather to act as an input to a key derivation function (KDF). That KDF uses the password as a starting point from which it will then generate the actual secure encryption key itself. Various methods such as adding a salt and key stretching may be used in the generation.
See also[edit]
- Cryptographic key types classification according to their usage
- Diceware describes a method of generating fairly easy-to-remember, yet fairly secure, passphrases, using only dice and a pencil.
- glossary of concepts related to keys
References[edit]
- ^'What is cryptography? - Definition from WhatIs.com'. SearchSecurity. Retrieved 2019-07-20.
- ^'Quantum Key Generation from ID Quantique'. ID Quantique. Retrieved 2019-07-20.
- ^Matthew Copeland; Joergen Grahn; David A. Wheeler (1999). Mike Ashley (ed.). 'The GNU Privacy Handbook'. GnuPG. Archived from the original on 12 April 2015. Retrieved 14 December 2013.
- ^Bidgoli, Hossein (2004). The Internet Encyclopedia. John Wiley. p. 567. ISBN0-471-22201-1 – via Google Books.
Cryptographic Key Management System
Retrieved from 'https://en.wikipedia.org/w/index.php?title=Key_(cryptography)&oldid=946641234'