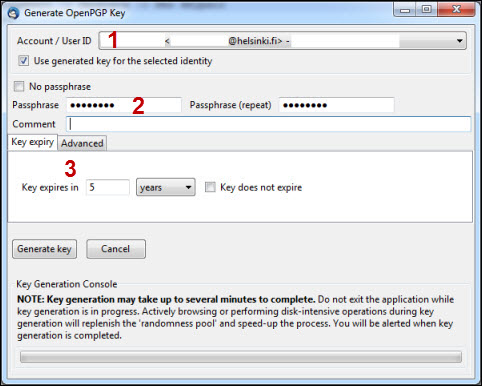
Gpg Generate Key With Passphrase
Previous: The quick key manipulation interface, Up: Unattended Usage of GPG [Contents][Index]
Apr 04, 2017 gpg -import bobpublickey.gpg Conclusion. Now we have notions on the principles to use and generate a public key. You know how GnuPG is functioning and you can use it for secure communication. GPG encryption is only useful when both parties use good security practices and are vigilant. Read Also: How to Encrypt/Decrypt File using GPG in Linux. CryptGPG does not yet support generating GnuPG keys. Generating a GnuPG key for use with CryptGPG is much the same as generating any other GnuPG key on a system. Though CryptGPG supports specifying the keyring to use, CryptGPG, by default, uses the keyring of the current user. The command -generate-key may be used along with the option -batch for unattended key generation. This is the most flexible way of generating keys, but it is also the most complex one. Consider using the quick key manipulation interface described in the previous subsection “The quick key. Your 'GPG key ID' consists of 8 hex digits identifying the public key. In the example above, the GPG key ID is 1B2AFA1C. In most cases, if you are asked for the key ID, prepend 0x to the key ID, as in 0x6789ABCD. Nov 14, 2019 Creating a GPG Key Pair. To start working with GPG you need to create a key pair for yourself. Use gpg with the -gen-key option to create a key pair.; With this option, gpg creates and populates the /.gnupg directory if it does not exist.; The secring.gpg file is the keyring that holds your secret keys; The pubring.gpg file is the keyring that holds your holds public keys. Apr 04, 2017 To encrypt your communication, the first thing to do is to create a new keypair. GPG is able to create several types of keypairs, but a primary key must be capable of making signatures. # gpg -gen-key Please select what kind of key you want: Your selection? 1 RSA keys may be between 1024 and 4096 bits long. What keysize do you want? Sometimes there is a need to generate random passwords or phrases automatically. We also offer an entirely browser-based secure online password/passphrase generator. Protecting a Private Key. The purpose of the passphrase is usually to encrypt the private key. This makes the key file by itself useless to.
4.5.4 Unattended key generation
The command --generate-key may be used along with the option--batch for unattended key generation. This is the mostflexible way of generating keys, but it is also the most complex one.Consider using the quick key manipulation interface described in theprevious subsection “The quick key manipulation interface”.
The parameters for the key are either read from stdin or given as afile on the command line. The format of the parameter file is asfollows:
- Text only, line length is limited to about 1000 characters.
- UTF-8 encoding must be used to specify non-ASCII characters.
- Empty lines are ignored.
- Leading and trailing white space is ignored.
- A hash sign as the first non white space character indicates a comment line.
- Control statements are indicated by a leading percent sign, the arguments are separated by white space from the keyword.
- Parameters are specified by a keyword, followed by a colon. Arguments are separated by white space.
- The first parameter must be ‘Key-Type’; control statements may be placed anywhere.
- The order of the parameters does not matter except for ‘Key-Type’ which must be the first parameter. The parameters are only used for the generated keyblock (primary and subkeys); parameters from previous sets are not used. Some syntactically checks may be performed.
- Key generation takes place when either the end of the parameter file is reached, the next ‘Key-Type’ parameter is encountered or at the control statement ‘%commit’ is encountered.
Control statements:
Print text as diagnostic.
Suppress actual key generation (useful for syntax checking).
Perform the key generation. Note that an implicit commit is done atthe next Key-Type parameter.
Do not write the key to the default or commandline given keyring butto filename. This must be given before the first commit to takeplace, duplicate specification of the same filename is ignored, thelast filename before a commit is used. The filename is used until anew filename is used (at commit points) and all keys are written tothat file. If a new filename is given, this file is created (andoverwrites an existing one).
See the previous subsection “Ephemeral home directories” for a morerobust way to contain side-effects.
This option is a no-op for GnuPG 2.1 and later.
See the previous subsection “Ephemeral home directories”.
This option is a no-op for GnuPG 2.1 and later.
Using this option allows the creation of keys without any passphraseprotection. This option is mainly intended for regression tests.
If given the keys are created using a faster and a somewhat lesssecure random number generator. This option may be used for keyswhich are only used for a short time and do not require fullcryptographic strength. It takes only effect if used together withthe control statement ‘%no-protection’.
General Parameters:
Starts a new parameter block by giving the type of the primarykey. The algorithm must be capable of signing. This is a requiredparameter. algo may either be an OpenPGP algorithm number or astring with the algorithm name. The special value ‘default’ maybe used for algo to create the default key type; in this case a‘Key-Usage’ shall not be given and ‘default’ also be usedfor ‘Subkey-Type’.
The requested length of the generated key in bits. The default isreturned by running the command ‘gpg --gpgconf-list’.
This is optional and used to generate a CSR or certificate for analready existing key. Key-Length will be ignored when given.
Space or comma delimited list of key usages. Allowed values are‘encrypt’, ‘sign’, and ‘auth’. This is used togenerate the key flags. Please make sure that the algorithm iscapable of this usage. Note that OpenPGP requires that all primarykeys are capable of certification, so no matter what usage is givenhere, the ‘cert’ flag will be on. If no ‘Key-Usage’ isspecified and the ‘Key-Type’ is not ‘default’, all allowedusages for that particular algorithm are used; if it is not given but‘default’ is used the usage will be ‘sign’.
This generates a secondary key (subkey). Currently only one subkeycan be handled. See also ‘Key-Type’ above.
Length of the secondary key (subkey) in bits. The default is returnedby running the command ‘gpg --gpgconf-list’.
Key usage lists for a subkey; similar to ‘Key-Usage’.
If you want to specify a passphrase for the secret key, enter it here.Default is to use the Pinentry dialog to ask for a passphrase.
An SSH key pair is a combination of a public key file and a private key file. Generate a 2048-bit public private rsa key pair kleopatra key. You can think of the public key as a lockon a door and the private key as the key that fits that lock.By default, SFTP Gateway disables password authentication and uses SSH key pairs as the primary authentication methodbecause they are more secure then passwords.There are a number of different types of ssh keys.
The three parts of a user name. Remember to use UTF-8 encoding here.If you don’t give any of them, no user ID is created.
Set the expiration date for the key (and the subkey). It may eitherbe entered in ISO date format (e.g. '20000815T145012') or as number ofdays, weeks, month or years after the creation date. The specialnotation 'seconds=N' is also allowed to specify a number of secondssince creation. Without a letter days are assumed. Note that thereis no check done on the overflow of the type used by OpenPGP fortimestamps. Thus you better make sure that the given value makesense. Although OpenPGP works with time intervals, GnuPG uses anabsolute value internally and thus the last year we can represent is2105.
Set the creation date of the key as stored in the key information andwhich is also part of the fingerprint calculation. Either a date like'1986-04-26' or a full timestamp like '19860426T042640' may be used.The time is considered to be UTC. The special notation 'seconds=N'may be used to directly specify a the number of seconds since Epoch(Unix time). If it is not given the current time is used.
Gpg Generate Key With Passphrase Free
Set the cipher, hash, and compression preference values for this key.This expects the same type of string as the sub-command ‘setpref’in the --edit-key menu.
Add a designated revoker to the generated key. Algo is the public keyalgorithm of the designated revoker (i.e. RSA=1, DSA=17, etc.)fpr is the fingerprint of the designated revoker. The optional‘sensitive’ flag marks the designated revoker as sensitiveinformation. Only v4 keys may be designated revokers.
This is an optional parameter that specifies the preferred keyserverURL for the key.
This is an optional parameter only used with the status linesKEY_CREATED and KEY_NOT_CREATED. string may be up to 100characters and should not contain spaces. It is useful for batch keygeneration to associate a key parameter block with a status line.
Here is an example on how to create a key in an ephemeral home directory:
If you want to create a key with the default algorithms you would usethese parameters:

Previous: The quick key manipulation interface, Up: Unattended Usage of GPG [Contents][Index]
To create a primary key In Object Explorer, right-click the table to which you want to add a unique constraint, and click Design. In Table Designer, click the row selector for the database column you want to define as the primary key. Right-click the row selector for the column and select Set. Primary key adalah.
- Table of Contents
- Generating a new keypair
- Exchanging keys
- Encrypting and decrypting documents
- Making and verifying signatures
GnuPG is a tool for secure communication.This chapter is a quick-start guide that covers the core functionalityof GnuPG.This includes keypair creation, exchanging and verifying keys, encryptingand decrypting documents, and authenticating documents with digitalsignatures.It does not explain in detail the concepts behind public-key cryptography,encryption, and digital signatures.This is covered in Chapter 2.It also does not explain how to use GnuPG wisely.This is covered in Chapters 3 and 4.
GnuPG uses public-key cryptography so that users may communicate securely.In a public-key system, each user has a pair of keys consisting ofa
The command-line option
You must also choose a key size.The size of a DSA key must be between 512 and 1024 bits, and an ElGamalkey may be of any size.GnuPG, however, requires that keys be no smaller than 768 bits.Therefore, if Option 1 was chosen and you choose a keysize larger than1024 bits, the ElGamal key will have the requested size, but the DSAkey will be 1024 bits.
Finally, you must choose an expiration date.If Option 1 was chosen, the expiration date will be used for both theElGamal and DSA keypairs.
You must provide a user ID in addition to the key parameters.The user ID is used to associate the key being created with a realperson.
GnuPG needs a passphrase to protect the primary and subordinate private keys that you keep in your possession.
After your keypair is created you should immediately generate a revocationcertificate for the primary public key using the option
Notes
[1]Option 3 is to generate an ElGamal keypair that isnot usable for making signatures.